Bitcoin’s peer-to-peer network is facing fresh scrutiny after a sharp rise in IP and IP-like addresses shared through ADDR messages.
Summary
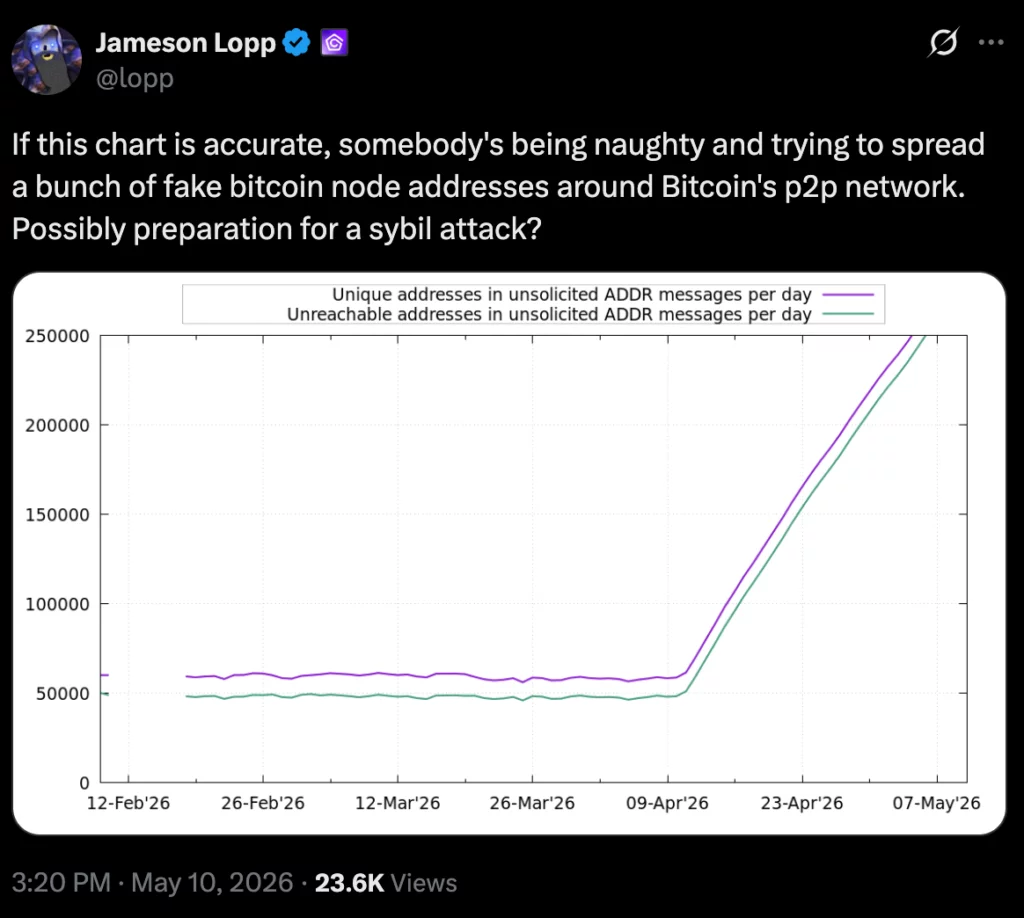
- Bitcoin’s gossip layer saw daily unique ADDR entries jump near 250,000 after years below 65,000.
- Jameson Lopp questioned whether fake node addresses could be preparation for a Sybil attack.
- The spike may also reflect surveillance, IP rotation, real node growth, or a public signaling push.
A live monitor maintained by researchers at Karlsruhe Institute of Technology showed daily unique addresses rising to about 250,000 after spending years below 65,000.
The spike started around mid-April 2026 and drew attention from Bitcoin developer Jameson Lopp. He questioned whether the data showed fake node addresses being spread across Bitcoin’s P2P network, calling it “possibly preparation for a sybil attack.”
ADDR messages help nodes find peers
ADDR messages help Bitcoin nodes learn about other nodes on the network. Bitcoin’s developer documentation says the addr message relays peer connection information and supports decentralized peer discovery across the network.
That system helps new nodes build connections and receive transactions and blocks. It also means poor or false peer information can create concern, since some control messages are not authenticated and can contain incorrect or harmful information.
Moreover, a Sybil attack occurs when one actor creates many fake identities to gain influence in a peer-to-peer system. Related crypto.news security background notes that a Sybil attacker can try to flood a network with fake nodes and isolate honest participants.
An eclipse attack is another concern. In that case, an attacker surrounds one node with controlled peers and gives it a limited view of the blockchain. Protos noted that Bitcoin Core has added protections such as address-table bucketing and ADDR rate limits, but no open network can remove every form of Sybil risk.
Other explanations remain possible
The address surge does not prove an attack. Protos noted that it could reflect real node growth, routine network changes, or broad IP rotation. Bitcoin is open and permissionless, so users can run nodes or rotate addresses without explaining why.
Surveillance is another possible explanation. Earlier crypto.news privacy coverage noted that researchers have studied deanonymization attacks on Bitcoin’s networking layer, including methods that try to link transactions to source IP addresses.
The debate also follows past disputes over Bitcoin node statistics. Protos reported that a September 2025 claim about suspected fake Bitcoin Knots nodes was later partly walked back after Start9 said many of the flagged nodes were regular customer devices.
crypto.news
#Bitcoin #node #flood #raises #fears #surveillance #Sybil #attack





